Endpoint security is a need and its motivation is to safeguard gadgets (endpoints) on an organization. Be that as it may, the expansion in refined digital assaults calls for further developed apparatuses and strategies for better endpoint security.
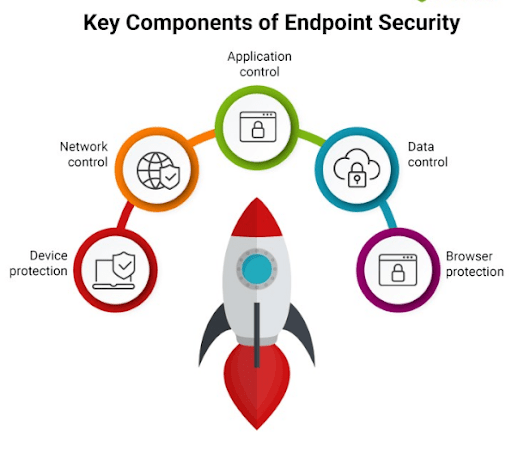
A normally powerful Endpoint Security Stage would contain the accompanying highlights:
Regulation with auto-sandboxing
Web URL Separating
Firewall
Antivirus
Cloud-based Record Query Administrations
Have Interruption Insurance Framework (HIPS)
Process Conduct Examination
While various instruments and procedures are accessible, endpoint security can be additionally improved with:
Network Access Control (NAC)
Information Misfortune Counteraction (DLP)
Information Obliteration
- 1D0-1053-23-D Exam Dumps (2024)
- 1D0-1054-23-D Exam Dumps (2024)
- 1D0-1055-23-D Exam Dumps (2024)
- 1D0-1056-23-D Exam Dumps (2024)
- 1D0-1057-23-D Exam Dumps (2024)
- 1D0-1058-23-D Exam Dumps (2024)
- 1D0-1059-23-D Exam Dumps (2024)
- 1D0-1060-23-D Exam Dumps (2024)
- 1D0-1061-23-D Exam Dumps (2024)
- 1D0-1064-23-D Exam Dumps (2024)
Information is put away on endpoints and clients associate with the endeavor network in numerous ways. Consequently, the organization should be shielded from potentially weak gadgets (endpoints) or gadgets that are now tainted and compromised. Also, there are a wide range of kinds of gadgets that require various sorts of safety.
Network Access Control (NAC)
Taking into account clients, gadgets and BYOD, NAC is a significant innovation for affirmation control. Security arrangements are characterized that guarantee that an endpoint meets characterized consistence levels before they are permitted to associate with the undertaking organization. Resistant gadgets are hindered. This element guarantees that the endpoints are protected from malware, and in the event that tainted they are not permitted to associate with the organization that might think twice about gadgets. The Lightweight Registry Access Convention (LDAP), RSA and Dynamic Index are used by NAC to organize the working of the firewalls and gadgets – switches and switches. This characterizes who is permitted network access and who isn’t. Better security is guaranteed. NAC can likewise be coordinated with cell phone the board (MDM) advances to actually look at cell phone security.
Information Misfortune Anticipation (DLP):
DLP devices can be coordinated into endpoint insurance suites or can be utilized as a different cloud-based instrument. These instruments shield the information on gadgets from unapproved pernicious clients attempting to access or take the information. It keeps delicate information from being moved out of the organization. Programmed debilitating of gadgets can be set off when dubious information move exercises happen. DLP apparatuses can be integrated into cell phone the executives answers for guaranteeing better security of cell phones.
Information Obliteration:
Unavoidably information must be put away on endpoints (counting cell phones). Regularly encryption ought to be executed in all gadgets however it may not be feasible for all gadgets. Be that as it may, when gadgets get lost, taken or are reassigned to one more client or venture, then the information on the gadget must be obliterated – totally erased.
At the point when information on hard plate drives and blaze drives are erased through typical orders, the information really doesn’t get erased. This information can be recuperated with effectively accessible programming devices. On the off chance that touchy venture information falls into some unacceptable hands, it can have serious ramifications. Thus, the hard plate drives and blaze drives should be accurately disinfected utilizing information cancellation instruments to annihilate the information totally. The Information Annihilation apparatus can be incorporated as a component of the MDM to guarantee upgraded endpoint security.